Download Extension dll for Windows 10, 8 1, 8, 7, Vista and XP
Dll ransomware is a dangerous and fast-spreading virus that is originating from the notorious Phobos ransomware family. It encodes sensitive users’ files using the strong encryption algorithms. As a result, all infected files can’t be accessed without a unique ID key.
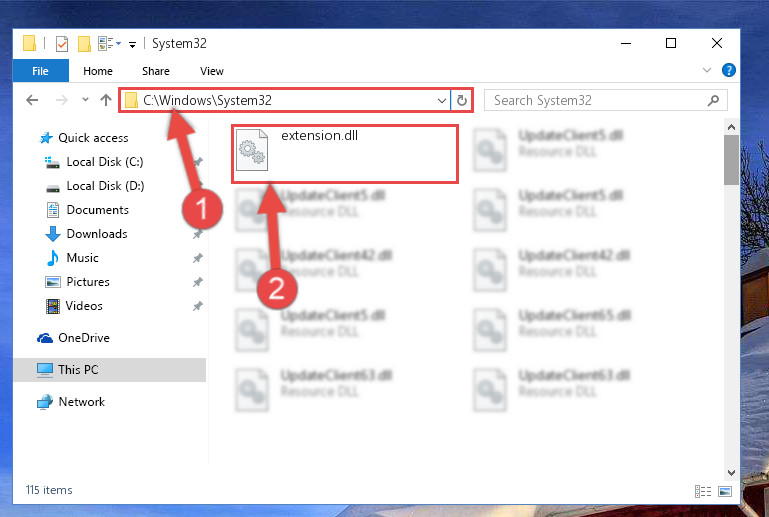
No its not a microsoft DLL, and its a software dll, i did reinstall but still didnt work so i need to download the dll. I personally wouldn’t download a DLL (especially if it’s a Microsoft DLL, i.e., part of Windows) from any website. I’d just run SFC and let Windows reinstall the DLL, that way you know it came from a safe source. If it’s a non-MS/Windows DLL, then you should be able to replace it by reinstalling the software that it was installed by. If you think you are infected, here are the steps needed to get your computer cleaned…. Restart your system after completing the steps to have all trace of the virus removed and to have your system updated.
Sppextcomobjhook.dll can indicate malware infection – remove it now
Easy to fix bug present as only source code for particular DLL needs to be fixed. DLL helps to modularized the applications and calls only when they are needed. DLL Show 2000 is a small system utility that displays a list of all running processes and their DLL dependencies. Anywhere PE Viewer is a free tool for exploring PE files .
- This depends on which company’s security software is installed by your users.
- You can find it in the confirmation e-mail you got after you purchased DLL-files.com Client.
- When performing this action, we will be able to access a dialog box.
- • Choose a name for the project, such as MyExecRefsDll, and enter it in the Name field.
Many programs are in fact so big that they have a central part which is always running and many optional extras. These are often called “plugins” and they work in a similar fashion. An EXE file can be run independently while a DLL is used by other applications.
Google Chrome to drop support for Windows 7/8.1
For example, a process may launch “cmd.exe” and not specify the full path. An attacker may put their own “cmd.exe” file in such a place that the innocent process will launch it before the official one. Other techniques exploit how Windows deals with spaces in the name in unquoted paths. You will receive mail with link to set new password. If you are still unable to rename the Windows defender folder in SAFEMODE, then we suggest you to please follow the following steps then try it again. The tool offers a series of options, such as “Context Menu,” “Aggressive Scan,” and “Smart Scan,” but without supporting documentation describing their respective functionalities.
Viruses on Windows Platforms
These damage routines are usually accomplished using ROM BIOS interrupts (e.g., 13h) and they will be successful. All software and driver updates that were installed on the computer, from the time it was first started, are lost. In this like-new condition, the computer is more susceptible to viruses because the added security updates have also been removed. The internet is filled with file sharing sites that offer cracks, keygens, and similar rogue software for millions of different programs. Additionally, file-sharing sites might be injected with malicious JavaScript that checks for users system vulnerabilities and then deploys exploit kits to insert malware automatically. Use reliable antivirus software to remove the malware from your computer.
Unwanted download and installation of malware is not the only problem caused by these tools. When a new virus variant is discovered, its signature is added to the signature database of the antivirus software. However, it has some limitations that enable threat actors to create advanced viruses that can avoid matching driversol.com/dll/kernelbase_dll with existing signatures. Simply put, an email virus is a malicious code or a link to malicious code sent via email.